Advanced Threat Hunting
What is Advanced Threat Hunting?
SOLUTION
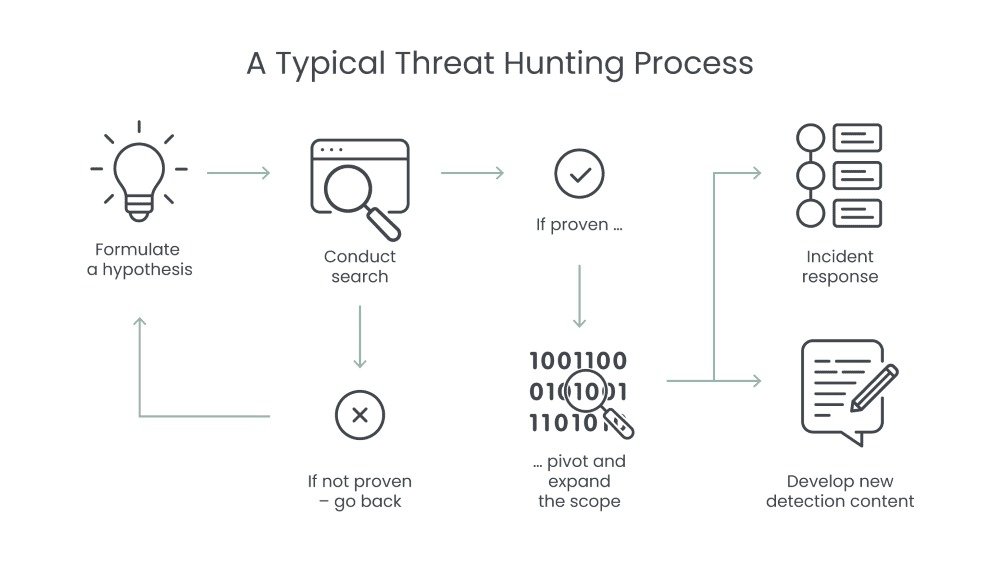
How Does Advanced Threat Hunting Work?
Active Searching
We don’t wait for an attack to happen. Our team actively searches through your systems, network, and data for unusual or suspicious behavior that could indicate a hidden threat.
Behavioral Analysis
We look for patterns in the way your network and devices are behaving. If something seems off—like unusual traffic or unexpected changes-we investigate further to identify any potential threat.
Finding Hidden Threats
Cybercriminals often use advanced methods to hide their attacks. We use sophisticated tools and techniques to find these hidden threats that may have slipped past regular security measures.
Immediate Action
If we find any signs of a potential attack, we respond quickly. Our team isolates the threat and works to remove it, preventing further damage to your systems and data.
Continuous Monitoring
Threat hunting is an ongoing process. We continuously monitor your network, always looking for new and evolving threats. This helps us stay ahead of hackers who are constantly finding new ways to attack.
