Vulnerability Scanning
What is Vulnerability Scanning?
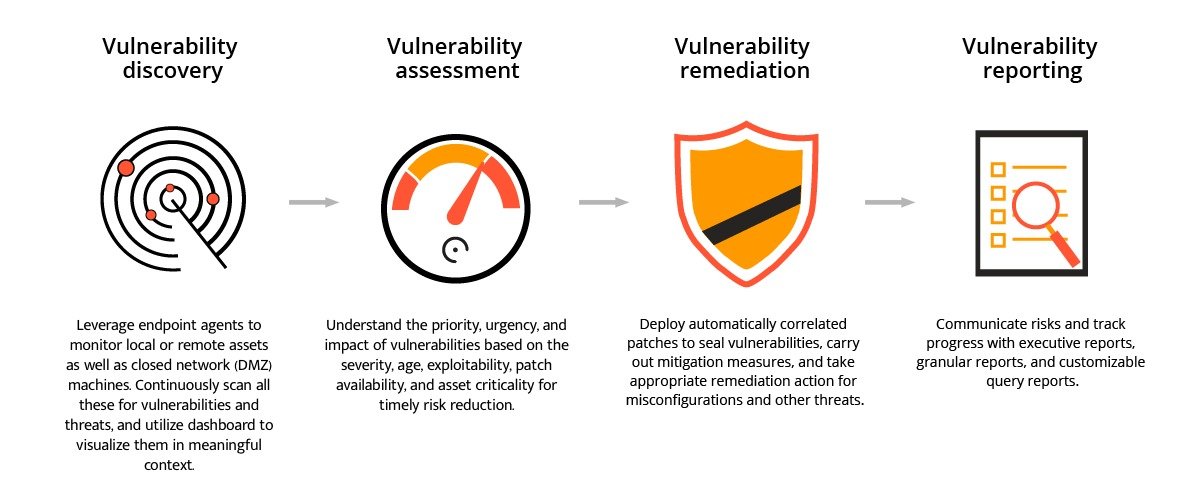
SOLUTION
How Does Vulnerability Scanning Work?
Automated Scanning
We use advanced scanning tools to automatically scan your entire network, systems, and devices. These tools are designed to find known vulnerabilities that could put your business at risk.
Identifying Weak Spots
If there’s any sign of a potential threat (like malware or ransomware), our EDR system quickly detects it and alerts our team. The faster we know, the faster we can stop it.
Automatic Response
During the scan, we look for security gaps such as outdated software, unpatched systems, misconfigurations, or exposed data that might make it easier for attackers to get in.
Detailed Reports
After the scan is complete, we provide a clear, detailed report showing any vulnerabilities found. This report explains the risk level of each issue and offers recommendations on how to fix them.
Ongoing Scanning
Cyber threats are always evolving, so we recommend regular scans to make sure your systems stay secure. With continuous scanning, we help you stay ahead of new vulnerabilities and risks.
Risk Prioritization
We help you focus on the most critical vulnerabilities first, ensuring that the most dangerous risks are addressed quickly. This minimizes the potential for harm.
